How to Protect Your Startup from DDoS Attacks with Flowtriq
The 2:00 AM Pager Scream: Why Infrastructure Fragility is Your Biggest Liability
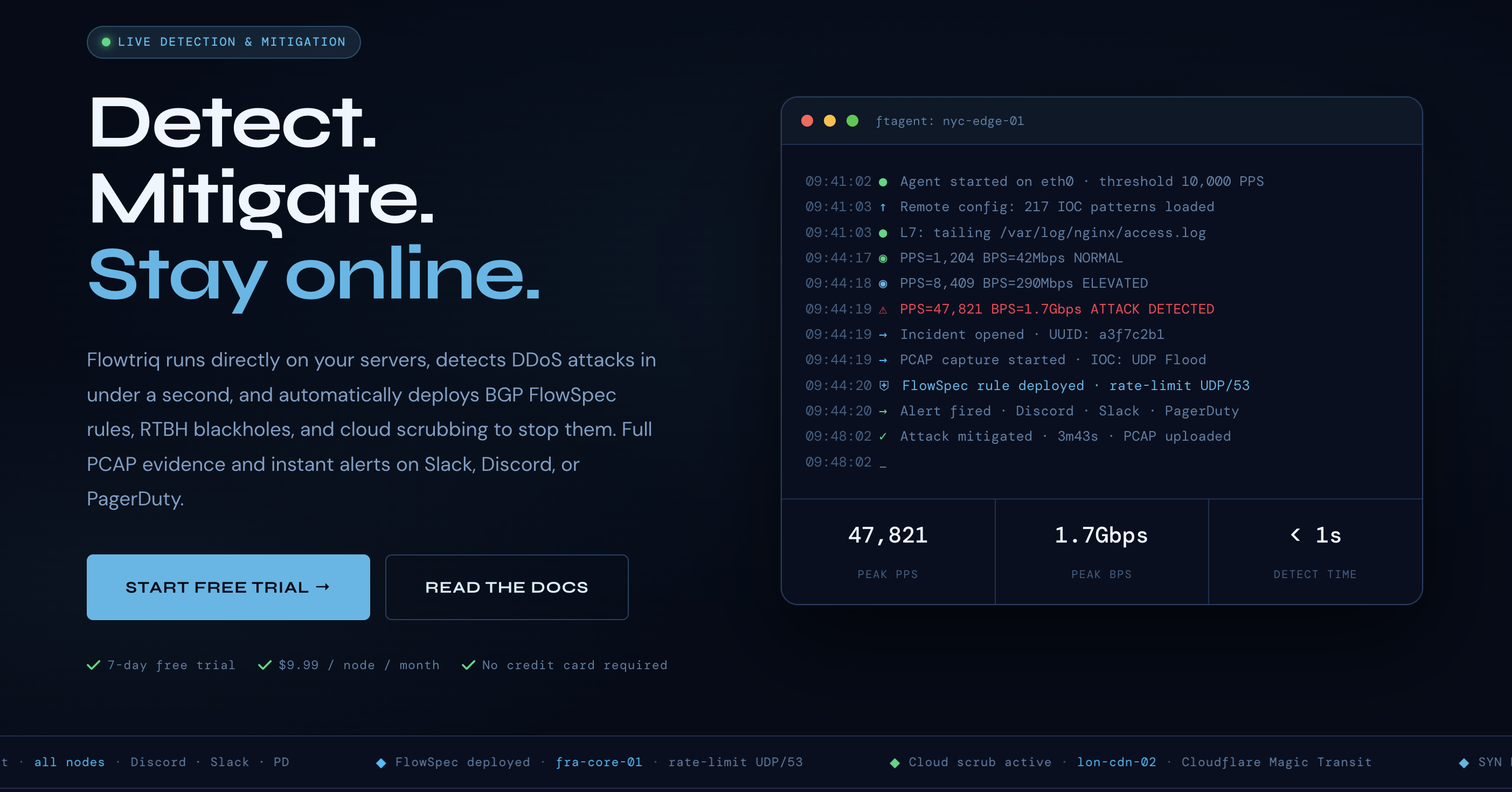
You know the drill—it’s 2:00 AM on a Saturday, your phone is screaming, and your Slack "incidents" channel is scrolling faster than you can read it. A massive UDP flood has just saturated your pipe, your upstream provider’s "auto-mitigation" is taking its sweet time to kick in, and your customer churn rate is ticking upward with every second of latency. For self-funded founders, a sustained DDoS attack isn't just a technical hiccup; it’s a direct hit to your burn rate and brand equity. Flowtriq is a lightweight, agent-based detection and auto-mitigation platform that halts these attacks in under one second. The bottom line: it transforms your defensive posture from reactive firefighting to automated, sub-second resilience.
The Business Case: Turning Uptime into a Competitive Moat
In my 15 years navigating the startup landscape, I’ve seen countless promising SaaS companies gutted by "noisy neighbor" issues or targeted extortion attacks. Traditional DDoS protection usually falls into two camps: the "Enterprise Tax" (paying five figures for hardware you don't fully control) or the "Black Box" (routing everything through a third party and praying their latency doesn't kill your UX).
Flowtriq shifts the ROI calculus by moving the intelligence to the edge. By installing a lightweight Python agent directly on your Linux nodes, you gain packet-level visibility without the overhead of heavy infrastructure. This is particularly vital for bootstrapped founders who need to protect varied workloads—from game servers to fintech APIs—without incurring the "traffic surcharges" that make scaling a nightmare. When you can mitigate an attack before it even hits your upstream’s threshold, you aren't just saving your servers; you’re protecting your LTV (Lifetime Value) by ensuring a seamless user experience during the exact moments your competitors are failing. This isn't just a security tool; it’s an insurance policy against reputation-killing downtime.
Key Strategic Benefits
- →Operational Efficiency: Flowtriq eliminates the "war room" fatigue by automating the response lifecycle. Instead of manual threshold tuning, the system uses dynamic baseline learning to understand your "normal," allowing your lean engineering team to focus on product shipping rather than monitoring pps (packets per second) graphs.
- →Cost Impact: With a flat-rate pricing model at $9.99/node, the predictable spend is a godsend for budget-conscious founders. By avoiding the per-gigabyte scrubbing fees common in the industry, you can scale your infrastructure horizontally without your security costs outstripping your revenue growth.
- →Scalability: The platform is built for multi-node management from a single pane of glass, making it as effective for a single edge node as it is for a 50-node cluster. As you grow from a handful of servers to a global footprint, the deployment remains a two-minute process that integrates into your existing CI/CD or configuration management scripts.
- →Risk Factors: While the sub-second mitigation is industry-leading, founders must ensure their escalation policies (BGP FlowSpec vs. Cloud Scrubbing) are correctly mapped to their specific upstream provider’s capabilities. Over-aggressive blackholing can lead to false positives if your baseline isn't properly established during the initial learning phase.
Implementation Considerations: From Vulnerable to Validated in 120 Seconds
From a strategic standpoint, the most compelling aspect of Flowtriq is the lack of "integration debt." Most enterprise security solutions require weeks of consulting and network topology changes. Flowtriq’s ftagent installs via a simple Python script on any Linux distribution.
The implementation timeline is essentially non-existent: you deploy, the agent begins "learning" your traffic patterns immediately, and you can have active mitigation playbooks running by the end of your lunch break. For leadership, the primary task is not technical oversight but rather policy definition. You’ll need to decide which "runbooks" trigger for specific attack vectors—for instance, using BGP FlowSpec for volumetric attacks while reserving cloud scrubbing for complex Layer 7 floods. Because the platform triggers full PCAP (packet capture) automatically during incidents, your post-mortem meetings will be driven by hard data and forensic analysis rather than "best guesses."
Navigating the Defensive Landscape
The DDoS mitigation market is crowded, and choosing the wrong partner can be an expensive mistake. On one end, you have the giants like Cloudflare and Akamai, which offer robust global scrubbing but can become prohibitively expensive and act as a "black box" regarding packet-level data. On the other end, infrastructure-specific solutions like OVHcloud's VAC provide solid protection but lack the granular, cross-provider orchestration that Flowtriq offers.
What sets Flowtriq apart—especially for the "Bootstrapper Weekly" audience—is the transparency. While competitors hide their threat intelligence, Flowtriq contributes back to the community, as seen with their recent Mirai botnet research (CVE-2024-45163). They aren't just selling a shield; they are providing the forensic tools (PCAP analyzers, BGP builders) that empower your team to understand the why behind the attack.
Recommendation: The Founder’s Action Plan
Security is often treated as a "tomorrow problem" until it becomes a "business-ending today problem." Don't wait for a ransom note or a service outage to audit your resilience.
- →Audit your current "Time to Mitigate": Ask your CTO how long it takes to detect and stop a 10Gbps UDP flood today. If the answer is "minutes," you are vulnerable.
- →Deploy a Pilot: Use Flowtriq’s 7-day free trial on your most exposed edge nodes.
- →Validate the Baseline: Review the traffic patterns after 48 hours to ensure the auto-learning matches your expectations.
- →Automate the Response: Link your Slack or PagerDuty to the dashboard to ensure your team sees the "Mitigated" alert before they even see the "Attack Detected" alert.